Accounts – OTP (MFA/2FA)
At the IPPP we have implemented Two Factor Authentication (2FA) also known as Multi Factor Authentication (MFA) utilising One Time Passwords (OTP), this is in line with University Policy. From here on will describe the IPPP MFA system as a One Time Password or OTP as to not confuse our system with CIS.
If you’re logged into an IPPP desktop then there will be fewer requests for your One Time Password than if you are accessing IPPP resources from elsewhere (e.g. CIS desktop, laptop on WiFi, Home or externally such as CERN).
How to Enrol an OTP
You will need to visit and login to our OTP service website at https://auth.ippp.dur.ac.uk/otp (which is only accessible via campus networks) using your IPPP login details.
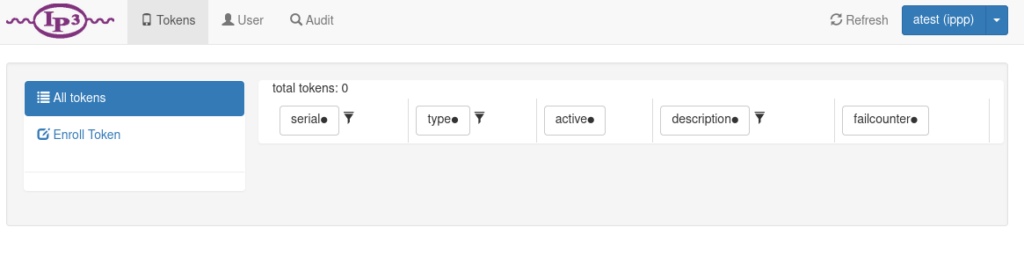
You should be greeted with an empty token list ready to enrol your own token.
TOTP Software (Recommended)
If you wish to use a TOTP we highly recommend using Microsoft Authenticator, FreeOTP or PrivacyIDEA apps.
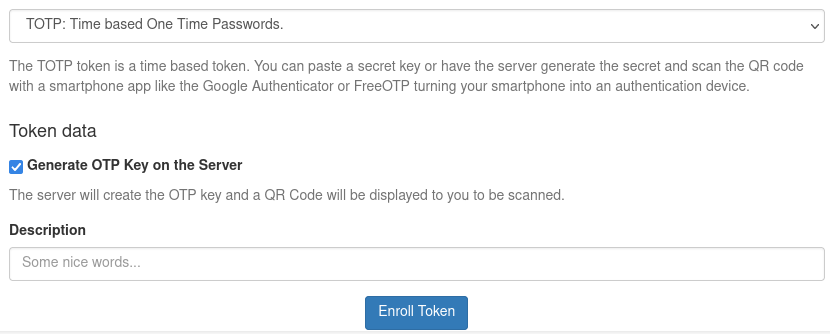
Please select “TOTP: Time based One Time Passwords.” from the drop down and provide a suitable description of your token, such as “Tim’s Mobile” if you were say Tim and using a Mobile app, then select “Enroll Token”.
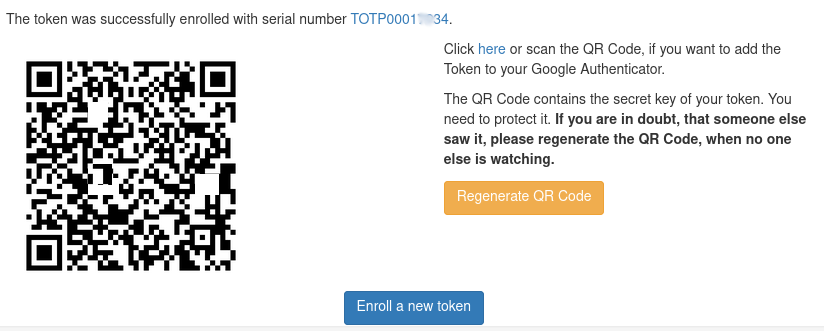
You will be then asked to scan the Token QR Code into your app, once this is scanned you can click then “Tokens” section on the top bar which will show you your tokens that you have enrolled.
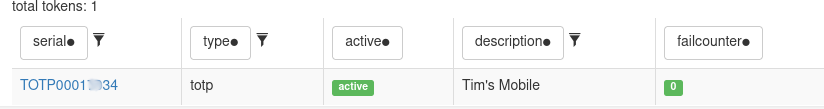
You should now see your newly enrolled token in the list so you’re now ready to use any service that requires an IPPP OTP.
TOTP Hardware (Recommended)
If you wish to use a hardware TOTP key then we can provide one of two styles, a Token for your keychain or a Token for your wallet in a credit card sized format.


These tokens are pre-enrolled and we simply assign the token to your user account.
If this is the solution you’d like then please get in touch.
YubiKey OTP
This is a hardware token that requires USB access to work, we do not recommend this for most users as future deployments might make this option much harder to work with. If you know this is the right solution for you then please get in touch. We may provide a guide on self-enrolment in the future.
PUSH
We currently do not recommend nor directly support this option.
Supported Types and Apps
| OTP | Type | Links |
| PrivacyIdea | Push & TOTP | Google Play, IOS App |
| Bitwarden Authenticator | TOTP | Google Play, IOS App |
| FreeOTP | TOTP | Google Play, F-Droid, IOS App |
| Microsoft Authenticator | TOTP | Google Play, IOS App |
| Google Authenticator | TOTP | Google Play, IOS App |
| Feitian C200* | TOTP Hardware | Contact Us |
| Token2 C202 | TOTP Hardware | Contact Us |
| Token2 Card | TOTP Hardware | Contact Us |
| YubiKey | Yubikey OTP Hardware | Contact Us, Find the right YubiKey |
*this is the hardware token currently provided by CIS.
Emergency Access
If you lose (or forget) your token we will have various methods to allow legitimate access to our systems without your original token but also ensuring the systems can remain secure. The method we chose will be case by case and situational per user.
What we do ask is that if you can disable or revoke the lost token ASAP or contact us to disable or revoke it on your behalf, this is to ensure the token can’t be used without your knowledge.
Self-Service
The ability to self service password resets as well as deploy your own OTP authenticator/tokens will be coming in the future.